Securing AWS S3 Websites Behind CloudFront

If you are hosting a site out of an AWS S3 bucket and serving up the content through Amazon’s CloudFront, you will almost certainly want your visitors to access the site through the CloudFront route rather than going directly to the Web endpoint on the S3 bucket. In this post, we’ll look at how we can easily restrict this backdoor access using an S3 policy.
Building and Leading an Effective Threat Modeling Program
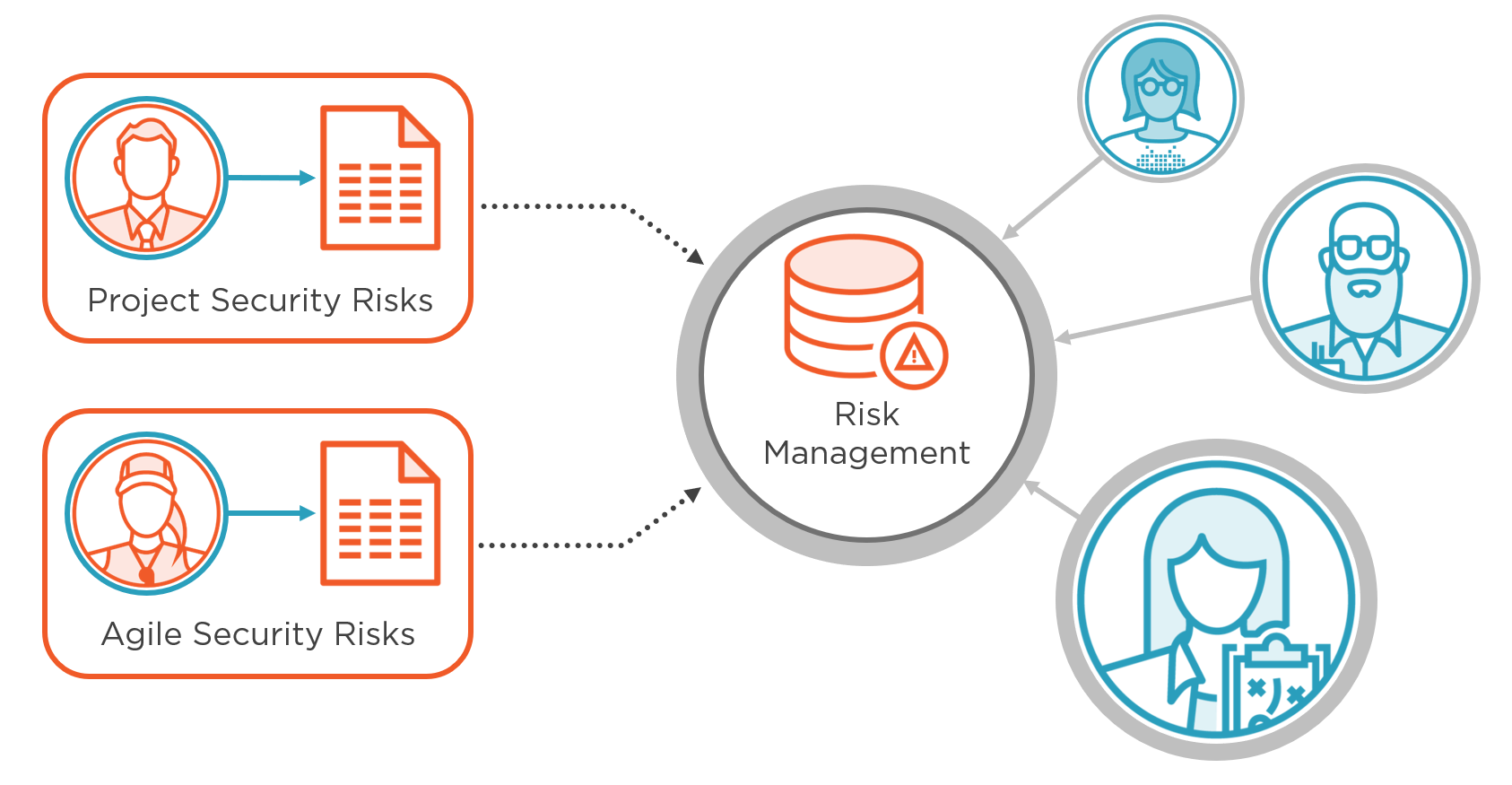
I’m pleased to announce that my course, Building and Leading an Effective Threat Modeling Program, is now live on Pluralsight.
Jump Starting Information Security Management

Do you need to establish your cyber defences in a hurry? In this article we’ll look at some techniques for getting immediate benefits from the implementation of an information security management system (ISMS).
Securing HL7

If you’ve worked with IT in the healthcare industry you’ll likely be familiar with HL7. HL7 V2 is the de facto standard for systems to exchange health information messages. The standard defines the type of messages and their structure but has little to say about how the information is secured. In fact, the standard explicitly states that information security is outside of its scope.